The MyVaydaTM Team
MyVaydaTM Story
MyVaydaTM came about after our co-founders saw customers overwhelmed with the proliferation of tools and technologies within their operational environments. Some with overlap within corporate security and risk management functions and duplication of efforts at times. This was seen in their former roles as senior leaders at leading services and solutions providers, and their time at the Big Four leading Security, Strategy, Risk Management and Cloud Services for Fortune 500 projects.
A common theme they saw was, overspend and underutilization of key tools and technologies, with a common theme of Security Leaders being asked to quantify security spend by senior executives and board of directors.
Whether building incident response programs, or leading technology and audit assessments, they have had that one moment where in order to complete an ask, they had to hunt down that one resource who held the knowledge to how a legacy system was configured and managed.
The thing is : attackers take advantage of these gaps and uncertainties or dependencies and companies are constantly trying to catch up.
With MyVaydaTM, we decided to take a different approach in terms of resolving some of the challenges we and our former industry colleagues faced, in running security technology businesses and operations.
This approach led to the development of this an easy-to-use platform that looks across siloes to calculate compound risk with artifacts and evidence for auditors.
Our Mission
To consistently deliver an industry-leading solution and service that harness unique, real-time insights into seamless, practical strategies; to solve today’s Identity related-Cyber risks, before they become tomorrow’s business problems.
Our Cultural Values
Humility: Ego doesn’t protect an organization.
Relevant Experience: Demonstrates real-world accomplishment.
Relationship: Collaboration, guided by a commitment to always put listening first.
MyVaydaTM IS MODULAR AND CAN BE DEPLOYED WITHIN A PRIVATE NETWORK OR CLOUD, OR CAN BE UTILIZED IN ITS SaaS FORMAT
MyVaydaTM
– Extracts risk telemetry from points solutions.
– Orients on identity as the systemic thread across transactions.
– Analyzes that identity behavior with pattern analysis to understand & assign inherent and residual risk.
– Aggregates risks across siloes to calculate compound risk for users/assets.
– Allocate/ componentize risks to precisely calculate and aggregate costs of security to accelerate risk-based decisions and capital investment.
– At the same time, it provides bidirectional feedback to source systems to enhance signal telemetry.
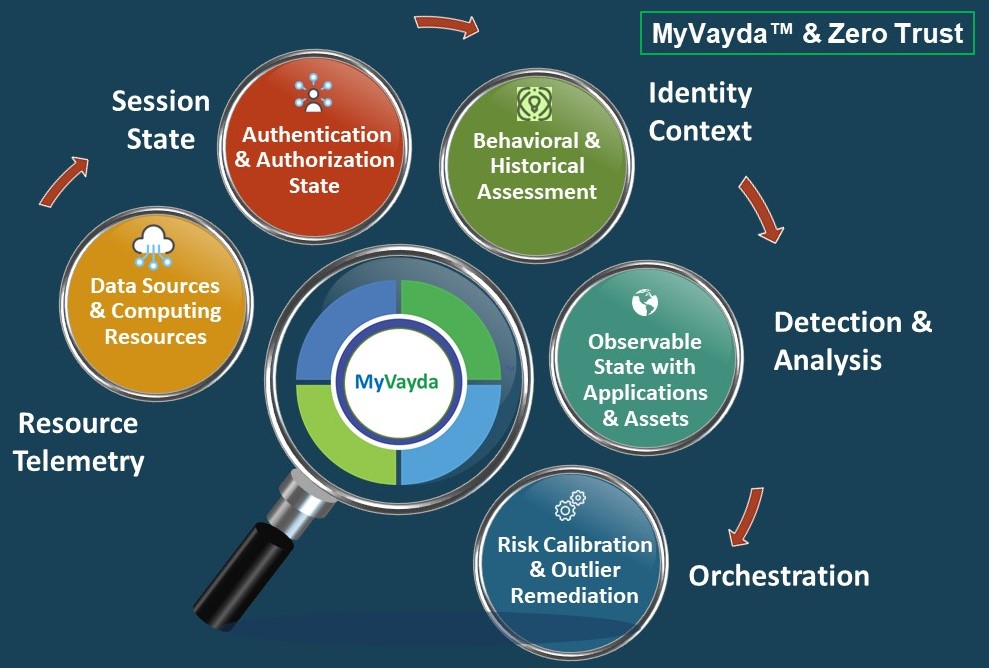
“Removing network location as a position of advantage eliminates excessive implicit trust,
replacing it with explicit identity-based trust.”
-Gartner, Market Guide to Zero Trust Network Access, June 2020